Blog
Ransomware Protection: Relying on Microsoft
By BUFFERZONE Team, 10/09/2017
With all the dangers to individuals and to organizations posed by ransomware, it’s no wonder that Microsoft has addressed the threat and attempted to secure Windows against it. And if the creators of our systems’ operating systems say they include protection, we should be able to rely on that protection, right?
Wrong.
Understanding CFA
In Windows 10, starting from version 1709 (released October 2017), and in Windows Server 2019 (released March 2018), Microsoft includes a new security feature called Controlled Folder Access (CFA). CFA appears under Ransomware Protection, as part of the Windows Defender Security Center:
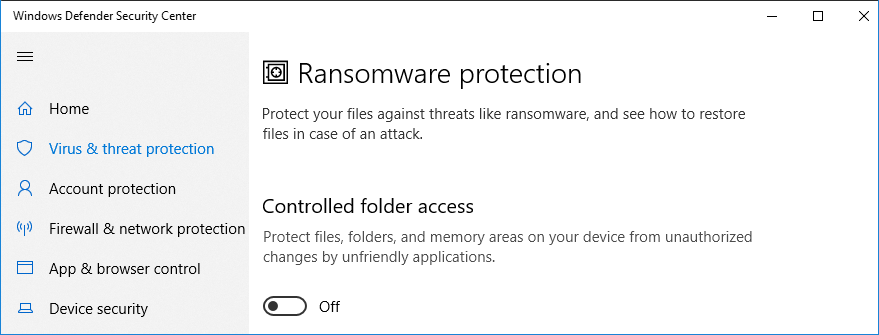
By default, CFA is disabled. Once you turn it on, CFA monitors programs that attempt to access files in protected folders, and allows write access only by known, legitimate programs. Protected folders are folders that are known to commonly contain personal or proprietary data, such as the Desktop and Documents.
You or your organization can add folders to be protected, and can add applications to the list of legitimate programs that are allowed to access the protected folders. In organizations, applications that are highly prevalent throughout the organization are automatically added to the list. Microsoft even provides a nifty Audit mode in which CFA just reports what it would block, without actually blocking anything. This lets you figure out which applications you need to whitelist before activating CFA.
In theory, CFA is a good idea. Let’s say some malware manages to infiltrate a network’s and a computer’s perimeter and endpoint defense systems, and attempts to encrypt data files in protected locations. Since its executable file is not recognized by CFA, it won’t be allowed to modify the protected files. Your data is safe.
Or is it?
CFA Limitations and Vulnerabilities
For starters, CFA is only aimed at protecting from one kind of ransomware – the kind that doesn’t block access to the computer system, only to specific files. Other ransomware, such as the infamous Petya malware (including its variant NotPetya), simply block access to the entire system until a ransom is paid. CFA doesn’t do anything to defend against these.
Additionally, the cyber criminals who produce even data-encrypting ransomware unfortunately don’t need to be too concerned about CFA. To them, CFA is just another security mechanism that they have several possible ways of circumventing.
For starters, CFA only if it works if it’s on. And if malware achieves administrative privileges on the computer, it can simply turn CFA off. Or, if it wants to be somewhat more stealthy, it can add itself to the whitelist of allowed applications.
Another approach cyber criminals can take is to piggyback on known, allowed applications and executables, which are generally legitimate but might be vulnerable to being compromised. Some such possibilities have been demonstrated by several researchers, including at the Nyotron Attack Response Center, as documented in their April 2018 report. These are:
- MS Office: Microsoft has whitelisted all Office applications for access to protected folders. So, Office macros or OLE objects could encrypt protected files.
- explorer.exe: APC injection can enable malware to be identified by CFA as the legitimate Windows Explorer executable.
- WMI: Malicious WMI scripts or applications are identified by CFA as legitimate, and do not require administrative privileges for modifying regular data files.
In reaction to some of these findings, Microsoft responded that these are not vulnerabilities of CFA, since CFA is meant only to provide a specific challenge to ransomware rather than generally prevent it. So, to our mind, not exactly ‘Ransomware Protection’.
Change the Approach
So what can you do? Stop relying solely on inspection-based security products that work by attempting to identify existing threats. Instead, use an isolation and containment product such as BUFFERZONE that isolates infectable areas from valuable resources.
BUFFERZONE creates a virtual container on organizational endpoints, and all processes that could access external, untrusted sources such as the internet are kept in the container, along with any data they download or save. At the same time, only uncontained processes can access trusted native endpoint and organizational files and other resources. The container is periodically wiped clean. So, even if ransomware does reach an endpoint, it can only encrypt recently downloaded files, for a short time, and is unable to do any real damage.
In fact, security experts both at BUFFERZONE and at one of the largest banks in Europe tested BUFFERZONE by intentionally infecting computer with various types of ransomware. Without performing any kind of inspection or signature identification, and without depending on anything unique to the tested ransomware, BUFFERZONE successfully contained the attack and the ransomware was unable to encrypt and lock any files outside the container.
Sources
Protect important folders with controlled folder access, on microsoft.com, May 8 2019
Vera Drobov & Daniel Prizmant, Windows 10 Controlled Folder Access Vulnerabilities, on nyotron.com, April 2018
Catalin Cimpanu, Researcher Bypasses Windows Controlled Folder Access Anti-Ransomware Protection, on bleepingcomputer.com, February 2018

















