Blog
BUFFERZONE ready to meet challenge posed by ransomware gangs combined efforts
By BUFFERZONE Team, 25/07/2022
A recent report indicates that ransomware criminals are working to together to spread laterally through hacked corporate environments.
The article suggests that the notorious Black Basta ransomware gang has partnered with the QBot malware operation, which is a Windows malware that steals bank credentials, Windows domain details and delivers further malware payloads on infected devices.
Victims usually become infected with Qbot via phishing attacks with malicious attachments. Black Basta is a relatively new ransomware operation that started impressively, breaching many companies in a relatively short time while demanding large ransom payments.
Analysts at the NCC Group discovered the new partnership between Qakbot and Black Basta during a recent incident response where they were able to identify the techniques used by the threat actor.
While ransomware gangs normally use QBot for initial access, NCC says that the Black Basta gang used it to spread laterally throughout the network. More specifically, the malware remotely creates a temporary service on the target host and configures it to execute its DLL using regsvr32.exe.
Once Qakbot is up and running, it can infect network shares and drives, brute-force AD accounts, or use the SMB (Server Message Block) file-sharing protocol to create copies of itself or spread via default admin shares using current user credentials.
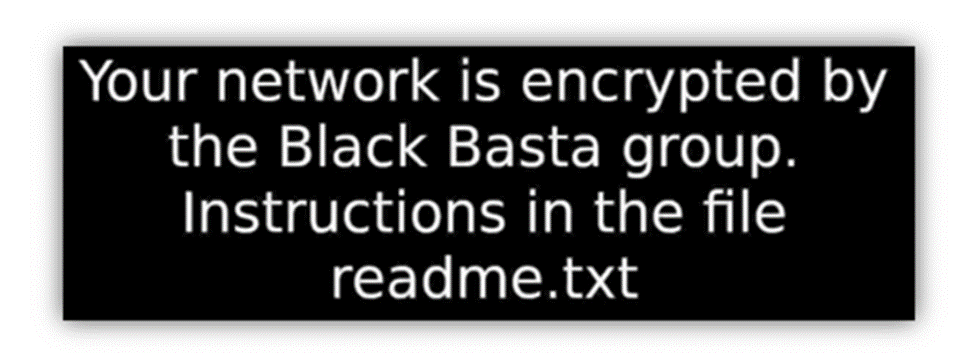
Desktop wallpaper image. Source NCC Group
“Qakbot was the primary method utilized by the threat actor to maintain their presence on the network. The threat actor was also observed using Cobalt Strike beacons during the compromise,” explains the NCC report.
The analysts also note that they discovered a text file named “pc_list.txt” in the Windows folder, which contained a list of internal IP addresses of all systems in the network, likely generated by Qakbot.
Although Qakbot possess a real challenge to organizations worldwide, BUFFERZONE offers an easy to deploy solution. The initial attachment in this phishing email is being sanitized or blocked by Safe Bridge. The Safe Bridge solution lets you safely share files download from the internet, without putting your organization at risk.
Safe Bridge provides users with content disarming capabilities, enabling disarming downloaded files and securely extracting them from the BUFFERZONE container. Browsing sessions that access external, untrusted content such as unknown internet sites are kept in a virtual container, protecting trusted resources from any potential threats.

















