BUFFERZONE® Safe Workspace® Solutions
To provide airtight security to users’ endpoints, from incoming content from risky sources, BUFFERZONE’s Safe Workspace® suite of protections intelligently combine automatic and manual virtual containment and disarming technologies in various ways. The specific protections depend on content source and type, and on Safe Workspace® edition, licensing, and configuration.
Safe Workspace® provides the following protections.
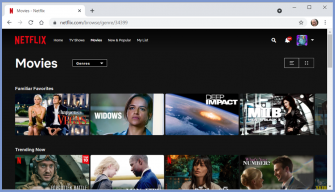
Safe Browser: Anti-malware
Safe Browser Anti-malware runs browser processes inside the Safe Workspace® isolated container, to protect the endpoint from malicious sites.
For user awareness, secured browser windows are bordered:
Downloaded documents and media files start out contained, and are then either disarmed of risky components or remain in the container.
Our SafeBridge® disarming engine supports almost all common document and media content types, and occurs automatically (in Safe Workspace® Pro edition; in Enterprise edition – depending on organizational policy).
Other downloaded files, such as executables, from well-known, trusted vendors – are trusted and allowed out of the container. Untrusted executables and other files remain contained; they appear in the designated Contained files local folder and are blocked from running, unless manually disarmed and uncontained (in Enterprise edition – as allowed by organizational policy).
Chrome, Edge, and Firefox are supported.
Safe Browser: Anti-phishing
Safe Workspace® Safe Browser anti-phishing combines multiple information sources and detection criteria with AI-based learning to determine if visited sites might be masquerading as other, reputable sites in order to steal submitted information.
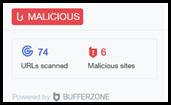
Uniquely, Safe Browser Anti-phishing utilizes BUFFERZONE® NoCloud® AI technology to minimize network latency and to increase user privacy by accelerating page analysis on the user endpoint.
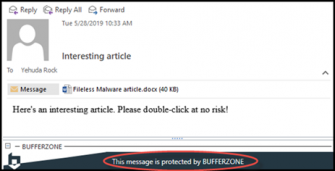
Safe Mail
In Outlook, Safe Workspace® Safe Mail disarms incoming message bodies by rendering inline images as HTML and blocking other inline attachments.
Upon double-clicking regular (not inline) message attachments, Safe Mail keeps the accessing process in its isolated container, and then handles the attachment files like Safe Browser downloads (as above).
[Web-based mail platforms such as Gmail and Outlook Web are secured by Safe Browser; Safe Mail is for the Outlook desktop application].
In Outlook, secured messages appear with an informative notification:
Safe Removables and External Sources
When a file is opened from USB memory or CD/DVD, Safe Removables keeps the accessing process in the Safe Workspace® isolated container, and then handles the file like Safe Browser downloads (as above).
USB flash drives and external drives are supported; access to phones as storage is blocked. USB Autorun is blocked.
With Safe Workspace® Enterprise edition, organizational policy can specify network locations or drive letters to be similarly secured.
SafeBridge®
Safe Workspace® includes SafeBridge®, which securely disarms downloads and attachments so they can be securely allowed out of the isolated container. SafeBridge® supports almost all common document and media content types.
With the Safe Workspace® Pro edition, disarming occurs automatically. With the Enterprise edition, organizational policy determines manual and/or automatic disarming, and can have files submitted for analysis and detection.
BUFFERZONE® Management Server (BZMS)
With the Safe Workspace® Enterprise edition, the BUFFERZONE Management Server (BZMS) provides centralized deployment and management of organizational Safe Workspace® agents, provides visibility to relevant organizational endpoints, and serves and assigns organizational policy by endpoint and/or user.

















